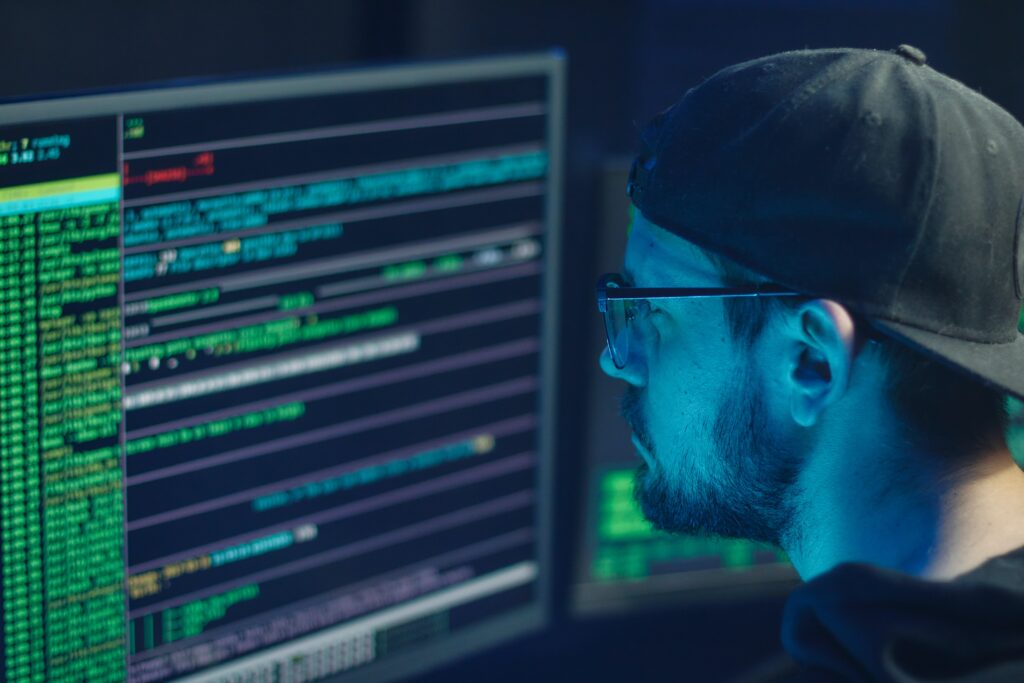
TryHackMe: The Story Behind
the UK’s Most Innovative
Cyber SME

source: infosecurity-magazine.com | image: pixabay.com
One of the many highlights of this year’s Infosecurity Europe 2022 event (21-23 June 2022) was the annual UK’s Most Innovative Cyber SME competition. The contest, run by the Department for Digital, Culture, Media & Sport (DCMS) and Tech UK in partnership with Infosecurity Europe, showcases the startup community’s enormous contribution to the UK’s booming cybersecurity sector. This is highlighted by the impressive list of previous winners, which include cybersecurity reskilling provider CAPSLOCK (2021), white hacking training platform Hack the Box (2019), communication security firm KETS Quantum Security (2018) and email security specialist Check Recipient (now trading as Tessian) (2017).
In the past two competitions, the judges have awarded first prize to companies involved in creating innovative solutions to resolve the much-publicized cyber-skills shortage, and this trend continued in 2022. The newly crowned winner of this award is TryHackMe, a cybersecurity training platform launched in 2018 that focuses on providing gamified lessons to its users. Once the celebrations had concluded, Infosecurity caught up with TryHackMe co-founder Ashu Savani to learn more about the company’s story, journey and future aspirations.
Savani described the application process for the Most Innovative Cyber SME competition as “very reflective,” allowing the team to reaffirm its goals following a whirlwind few years. “The application process was quite fun as it solidified our mission and the work we’re doing in our mind,” he explained. “We were very excited to be accepted as it gave us recognition for the work we are doing, which is to make it as easy as possible for anyone to learn cybersecurity, whether you’re a construction worker or a school teacher.”
Did he expect TryHackMe to win though? “We weren’t sure we were going to win; we were just really happy that we got through to the final and got a chance to give TryHackMe more exposure,” Savani replied modestly. Win they did though, and the award represented the culmination of many years of hard work, challenges and innovative thinking.
The Beginnings
The idea for TryHackMe was born after Savani met co-founder Ben Spring during a summer internship at the consultancy Context Information Security. “It was during the internship that we realized there isn’t a lot of cybersecurity learning material,” and most of it was orientated towards people already proficient in security, which, Savani explained, “isn’t very conducive to learning security.”
Spring began a side-project that involved building systems on the cloud. He then suggested the idea of adding training material and notes to Savani. “That ended up being the very early prototype of TryHackMe, where you could launch training material with a touch of a button and have some sort of learning focus there,” explained Savani.
As the pair developed the prototype, they put the word out on platforms heavily used by the amateur hacking community like Reddit, “and people started using our products.” This was the motivation to keep developing the product, carefully incorporating user feedback. “Fast-forward four years, and we’ve been very fortunate to have a loyal user base still using us. We believe we’re positively contributing to closing the cyber skills gap and we’re excited to continue doing that work,” said Savani.
Overcoming Challenges
As with all startups, there were significant challenges and bumps in the road to overcome in the early years. One of the key difficulties for TryHackMe was acquiring users beyond its base. After attempting a number of different strategies, the company found the most effective approach was holding events that allowed the participants to win prizes by competing in cybersecurity challenges. This included partnering with universities through events called ‘HackBack.’
The other major challenge was building out the product “sustainably,” which required hiring the right people to develop and scale the business. “It’s one of those things that’s tough to solve overnight,” reflected Savani. However, they now have “some really amazing people” on board. “We’ve been very fortunate to bring on people who love teaching and have that cybersecurity experience,” he noted, adding: “All our different pockets and departments at TryHackMe have an impact on the work we’re doing on a day-to-day basis.”
In terms of the training platform’s evolution, there has been a strong emphasis on gamification, which TryHackMe found most effective in engaging users. “We’re focusing on ensuring the users enjoy the material and stick to what they’re doing.”
Savani also revealed the company is now looking to expand its material, providing relevant training content for experienced professionals as well as beginners in the field of cybersecurity, which was previously the primary focus. This includes moving into “more intermediate to advanced topic areas for things like DevSecOps, red teaming and blue teaming.”
Long-Term Vision
Savani emphasized that while the training content is designed to be fun and engaging, it must have practical real-world benefits for the users. The ultimate vision is “to take a student with a little technical experience all the way to an advanced consultant who understands the complex concepts within defensive security.” Savani added that it is also increasingly working with businesses to train their security teams, “an area we’re looking to grow.”
In addition to the quality of the TryHackMe service, Savani acknowledged that the company’s core focus on reducing barriers to entry in cybersecurity was a crucial factor in being crowned Most Innovative Cyber SME at Infosecurity Europe 2022. Lack of diversity and accessible pathways are a major blockage to addressing the cyber skills gap, and TryHackMe is making a conscious effort to provide an opportunity to train in cybersecurity, regardless of background and ability to pay. The firm currently has a pricing scheme of £8-10 ($9.50-12) a month. “No one should be paying lots of money just to discover whether cybersecurity is a feasible career for them,” he added.
Looking ahead, the long-term vision for TryHackMe is to continue its mission to provide affordable and engaging training for those looking to develop a career in cybersecurity. This involves constant reflection and evolution, taking on user feedback to continuously improve the platform.
Solving the cyber skills shortage is a long-term challenge for the industry and requires innovative ideas and approaches. Often, startups have the most ‘out-of-the-box’ solutions, and TryHackMe has demonstrated this trait over its first few years of operation. TryHackMe’s triumph in this year’s contest, alongside other recent victors, shows that this issue is being taken increasingly seriously in the cybersecurity sector.