Facebook’s In-app Browser on iOS Tracks ‘Anything You Do on Any Website’

source: threatpost.com | image: pixabay.com
Researcher shows how Instagram and Facebook’s use of an in-app browser within both its iOS apps can track interactions with external websites.
Users of Apple’s Instagram and Facebook iOS apps are being warned that both use an in-app browser that allows parent company Meta to track ‘every single tap’ users make with external websites accessed via the software.
Researcher Felix Krause, who outlined how Meta tracks users in a blog posted Wednesday, claims that this type of tracking puts users at “various risks”. He warns both iOS versions of the apps can “track every single interaction with external websites, from all form inputs like passwords and addresses, to every single tap” via their in-app browsers.
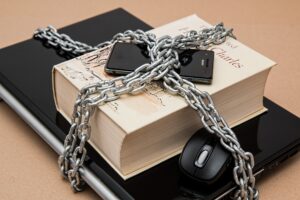
iOS users’ concerns over tracking were addressed by Apple’s 2021 release of iOS 14.5 and a feature called App Tracking Transparency (ATT). The added control was intended to require app-developers to get the user’s consent before tracking data generated by third-party apps not owned by the developer.
Krause said that both iOS apps Facebook and Instagram are using a loophole to bypassed ATT rules and track website activity within their in-app browsers via the use of a custom JavaScript code used in both in-app browsers. That means, when an iOS user of Facebook and Instagram click on a link within a Facebook and Instagram post (or an ad), Meta launches its own in-app browser which can then track what you do on external sites you visit.
Meta’s Use of a JavaScript Injection
“The Instagram [and Facebook] app injects their JavaScript code into every website shown, including when clicking on ads. Even though pcm.js doesn’t do this, injecting custom scripts into third party websites allows them to monitor all user interactions, like every button & link tapped, text selections, screenshots, as well as any form inputs, like passwords, addresses and credit card numbers,” Krause wrote.
Continue reading “Facebook’s In-app Browser on iOS Tracks ‘Anything You Do on Any Website’”